We’ve come a good distance since 1993, when Peter Steiner’s now-infamous and oft-cited ‘On the Web, no one is aware of you’re a canine’ cartoon hit the pages of The New Yorker.
Today, nonetheless, there are most likely fairly a number of folks on the Web who’ll have a good suggestion in case you’re a canine. They most likely additionally know, or might simply discover out, your identify, what you seem like, the place you reside, the place you're employed, your date of beginning, the identify of the primary college you went to, and possibly your mom’s maiden identify as effectively.
If that sounds horrifying, then maybe it ought to be – id fraud accounted for 68% of instances filed to the Nationwide Fraud Database in 2022, and nearly all of these instances (86%) resulted from on-line interactions, in response to Cifas, a cross-industry UK fraud prevention service.
If somebody does handle to piece sufficient info collectively about you, they will open financial institution accounts in your identify and use them for cash laundering, apply for loans and extra. You'll then be chased to pay again these loans, and the police would possibly suppose you are the one chargeable for cash laundering. Sorting this out and proving it wasn’t you may take time, contain a number of stress and will even value you your job. Id theft can break your life, so defending your id ought to be a high precedence.
And it isn’t simply fraudsters who is likely to be after your info. Being lax about privateness and safety on-line means you would inadvertently arm nearly anybody with details about your pursuits and whereabouts, from that one who used to terrorise you in school who now retains making an attempt so as to add you on Fb, to a vindictive ex-partner, or that terrible fleeting acquaintance who retains making an attempt to get you to endorse them on LinkedIn (in case you’re studying this, please go away me alone).
Thankfully there are various instruments at your disposal to assist higher shield your on-line id, in addition to adopting some finest practices and taking proactive steps. Listed here are the primary ones you need to learn about – and put into motion!
1. Use a password supervisor
A method folks can get to your private info is by guessing your passwords and logging into accounts that include that info.
Sustaining separate passwords for every account you employ is a drag, to not point out impractical.
You might give you sturdy and distinctive passwords for every part that requires one, and possibly even write these down on a chunk of paper, or in a pocket book, and preserve that someplace protected. That, clearly, isn’t handy for occasions if you’re out and about.
You could possibly in concept take that pocket book with you, however, after all, in case you lose your pocket book, you then’ve bought to reset passwords for every part and begin once more. If it’s stolen, then, effectively, you’ve simply given whoever’s stolen it a veritable goldmine of data.
You could possibly additionally use a third-party service corresponding to Fb or Google to signal into different apps and companies – a extra handy resolution, however then, after all, you’re giving Fb and Google, or whoever, an excellent larger concept of your shopping and spending habits.
A extra sensible possibility is to make use of a password supervisor, an app which shops and encrypts login particulars for each service you employ behind a single, sturdy grasp password.

Jim Martin / Foundry
One of the best password managers can shield your accounts with biometric logins which means you need to use fingerprint scanners and front-facing cameras in your cellphone, laptop computer, or PC to verify that it's certainly you that’s logging in, and never another person.
password supervisor may even assist multi-factor authentication by default, which suggests if you accurately enter your grasp password, you’ll even be required to enter an extra code, securely despatched to you thru one other app. Talking of which…
2. Use two-factor or multi-factor authentication
Two-factor authentication, generally expressed as ‘2FA’, or generally ‘two-step verification’, is a straightforward however efficient means of including an additional layer of safety to any account you recurrently check in to.
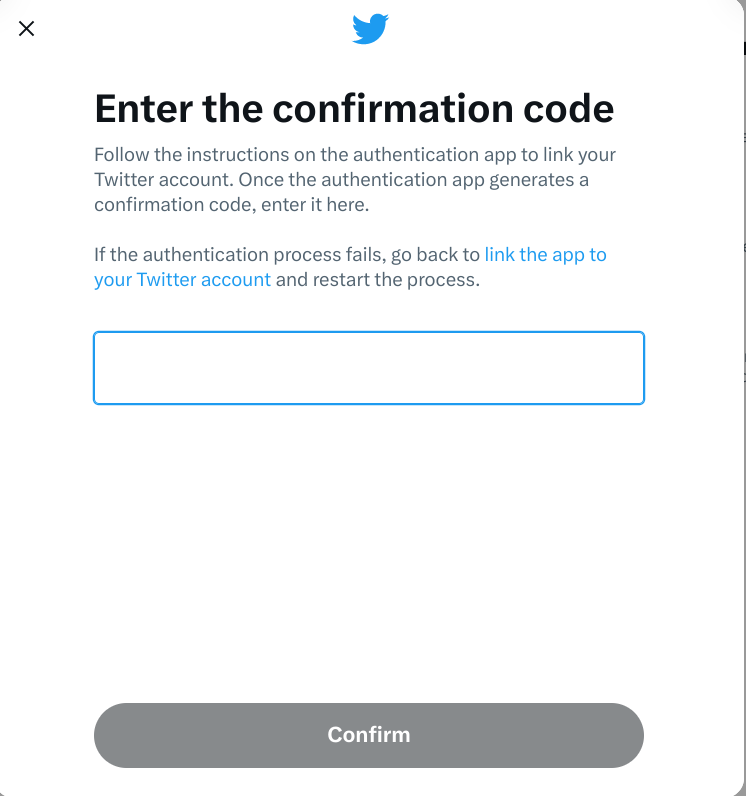
IDG / Ashley Biancuzzo
With two-factor authentication arrange, when you’ve entered your password – the primary issue of authentication – you’ll be despatched a 4 or six digit code to enter as effectively – the second issue of authentication.
Should you don’t have entry to that second code, you then’re not getting in. Which means it doesn’t matter if somebody has accurately guessed your password: they nonetheless can’t entry your account.
One of the best method is to have authentication codes despatched to you through an authenticator app, corresponding to Authy, Duo Cell, Google Authenticator, or Microsoft Authenticator. Some password managers, like Dashlane and 1Password, include their very own built-in authenticators.
You could possibly additionally contemplate investing in a safety key. These {hardware} gadgets should be plugged into one among your laptop computer’s USB port, or tapped in your cellphone to authenticate through NFC. You must watch out to not lose them, very like your own home keys, and so they’re not supported by all that many companies on-line.
Safety key choices embrace Yubico’s YubiKey 5C, CryptoTrust’s OnlyKey, and Thetis’s FIDO2.
3. DON’T have authentication codes texted to you
Whereas 2FA is a good concept in concept, in follow, it’s not a good suggestion to have firms textual content you authentication codes.
The rationale for that is easy: SMS textual content messages may be intercepted, and it doesn’t require expensive gear or in depth technical information to take action. As soon as somebody has your authentication code, then they may very effectively acquire entry to numerous issues; your on-line checking account or funding portfolio, or no matter you’re making an attempt to log in to.
If a service helps 2FA, you need to examine if you need to use an authenticator app as a substitute having codes through textual content/SMS.
Alternatively, there is likely to be an choice to be despatched authentication codes through electronic mail as a substitute. That’s a safer possibility, as your electronic mail supplier ought to be encrypting messages in transit as normal. Nevertheless, in case your electronic mail account is compromised, you then’re in danger.
Because of this, it’s good follow to mechanically delete any sort of authentication electronic mail that’s despatched to your account.
4. Use a VPN
A VPN (Digital Non-public Community) is an efficient means of securing your on-line exercise, as a VPN encrypts all your community visitors, stopping anybody from preserving a log of your on-line classes.
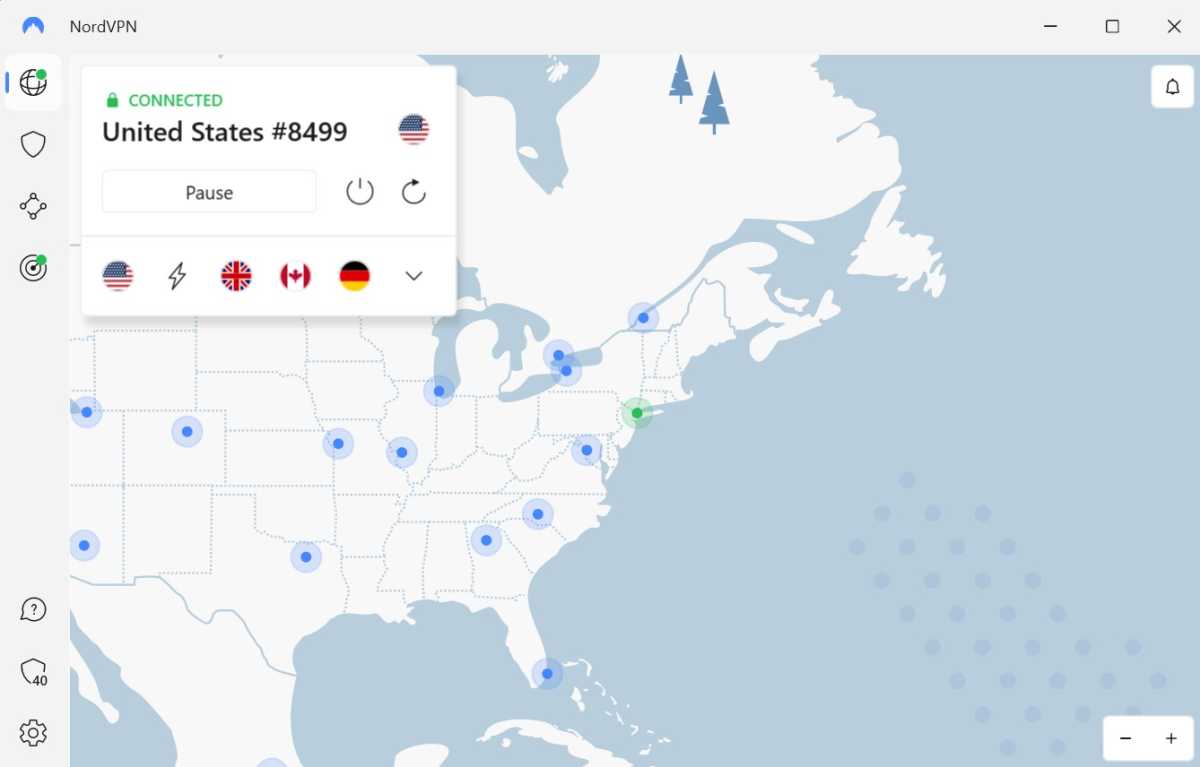
Anyron Copeman / Foundry
Nicely, virtually anybody – the one organisation that would know which websites and companies you go to and log in to is the VPN supplier itself.
Because of this, when procuring round for a VPN supplier it is very important examine to see if the VPN supplier operates a strict ‘no connection logs’ coverage, and, extra importantly, if that coverage has been independently verified.
VPNs which have made the grade on this regard in our most up-to-date spherical of testing embrace NordVPN, CyberGhost, and PureVPN – see our round-up of the most effective VPN companies for a full breakdown.
5. Use burner electronic mail tackle
Whereas newsletters may be nice methods of discovering out about promotions and getting some money-off vouchers, it is likely to be a good suggestion so that you can signal as much as these utilizing a devoted electronic mail tackle, as a substitute of your foremost one.

Foundry / IDG
Whereas 2-for-1 offers and low cost pizzas are nice, what’s not nice is when advertising and marketing firms share subscriber info with knowledge brokers, which may result in you being despatched a number of advertising and marketing emails for stuff you by no means even signed up for within the first place, or aren’t even desirous about.
Whereas that in itself isn't an inherent safety threat, what it will probably do is make it tougher so that you can spot rip-off emails and comparable phishing makes an attempt, which regularly disguise themselves as respectable advertising and marketing emails. Plus, who desires unsolicited mail? No-one.
If all advertising and marketing visitors is funneled in direction of a selected electronic mail account, it leaves your mail account with emails you would possibly really wish to learn.
6. Ask knowledge brokers to delete info they maintain on you
Knowledge brokers, corresponding to Acxiom, Equifax, Experian, and TransUnion generate profits from promoting details about you to advertising and marketing firms.

Tech Advisor/Foundry
Details about you may come from a wide range of sources, from firms promoting your knowledge to 3rd events as described above, from analysing your net shopping historical past, and your procuring historical past.
Whereas the UK has now left the European Union, the phrases of the EU’s GDPR (Normal Knowledge Safety Regulation) nonetheless applies.
Below Article 21 of the GDPR, you may order firms to cease processing any private knowledge they maintain on you for the needs of selling, and beneath Article 15, you will have the precise to make an SAR (topic entry request), the place an organization should share all and any private knowledge they maintain about you, without cost.
Within the U.S. your rights presently fluctuate from state to state, however you continue to could also be profitable in contacting an organization or organisation with an SAR – or SRR (topic rights request) as they’re additionally identified. U.S. primarily based non-profit Privateness Rights Clearninghouse maintains a listing of information brokers, which states they’re situated in, and whether or not or not they permit an decide out.
As per the Australian Privateness Act, you may request entry to the info that an organization holds on you, and request to appropriate any incorrect info, delete it or de-identify it, whether it is now not required for his or her functions.
With a view to make any sort of entry request, you will want to offer some fundamental info – corresponding to your identify, residence tackle, cellphone quantity electronic mail tackle – and probably some supplementary info, corresponding to your account identify/consumer ID, in order that an organization can accurately determine you and course of your request.
You too can pay third events to contact knowledge brokers in your behalf, in case you are quick on time – organisations providing such a service embrace DeleteMe, Incogni, OneRep, OptOutUK, and PrivacyBee.
Nevertheless, knowledge brokers might not reply to requests made on behalf of people by third events corresponding to these. It is likely to be that an organization can solely let you know who holds knowledge about you – through which case it could then be as much as you to contact the corporate, and request that they delete any knowledge held on you.
7. Lock down or delete social media accounts
Along with eliminating the inevitable cringe posts and pictures of you with regrettable haircuts/outfits/each, closing or deleting previous or inactive social accounts and blogs may be a good suggestion, particularly in the event that they include something too private.

Hannah Cowton/Foundry
Whether or not it’s damaging to your fame or private credibility or not, there’s info you’ve posted on the market on a platform you’ve not up to date or maintained for numerous years, there’s an opportunity that somebody might acquire entry to your profile. It is best to purge any previous accounts, particularly if they're nonetheless linked to an energetic electronic mail tackle.
Briefly, in case you’re now not utilizing Fb, Twitter, Instagram, or any sort of platform, contemplate deleting it, or, on the very least, lock down the privateness settings to regulate who can see that knowledge. That means you continue to keep a presence on these platforms, however they’re a lot much less seemingly for use by anybody making an attempt to impersonate you.
8. Don’t share an excessive amount of on-line
Comic Stewart Lee as soon as memorably described Twitter as “the Stasi for the Offended Birds era”, and famously doesn't keep a private social media presence.

Tech Advisor/Foundry
Whilst you may not wish to make use of the identical method to social media as Mr. Lee, his foremost level about revealing one’s whereabouts and habits on a public on-line platform like Twitter is price preserving in thoughts.
Posting a photograph of you in entrance of the home you’ve just lately moved into, then later complaining that your landlord nonetheless hasn’t fastened that downstairs window, after which saying to the world that you simply’re about to go on vacation for a few weeks, might all add as much as you coming again residence to a nasty shock.
9. Choose out of sharing knowledge
Lastly, learn the phrases and situations of the stuff you join, and decide out of information sharing the place you may. It’s tempting to click on or faucet by means of the welcome or set up screens with out paying any consideration to what they’re saying. Very often you will have the chance to restrict the info you share with that firm, however you have to learn these screens to know if you have to tick a field or click on the Decline button.
Additionally, average what you share on-line, and be savvy about how somebody taking a look at your profile would possibly be a part of the dots. Use some type of multi-factor authentication, however don’t have codes despatched to you through SMS if in any respect attainable, and think about using a password supervisor and a VPN to higher shield your self and your on-line exercise.


